Kyber Network Warns Elastic Liquidity Providers of Potential Vulnerability - Crypto News - Unchained

Elastic on X: "Update: Read our blog for additional detection and threat hunting improvements on the #Log4j2 vulnerability: https://t.co/O0jfeJg0S5" / X



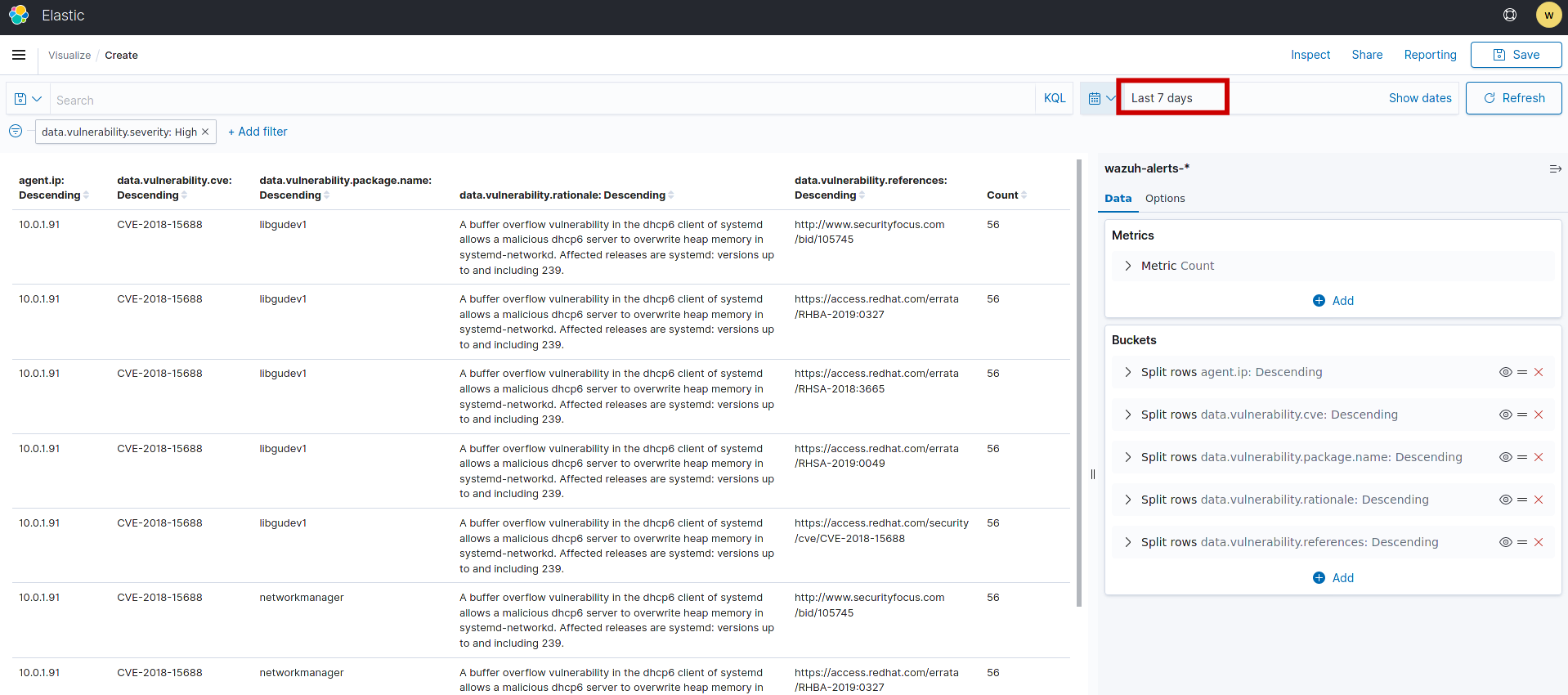






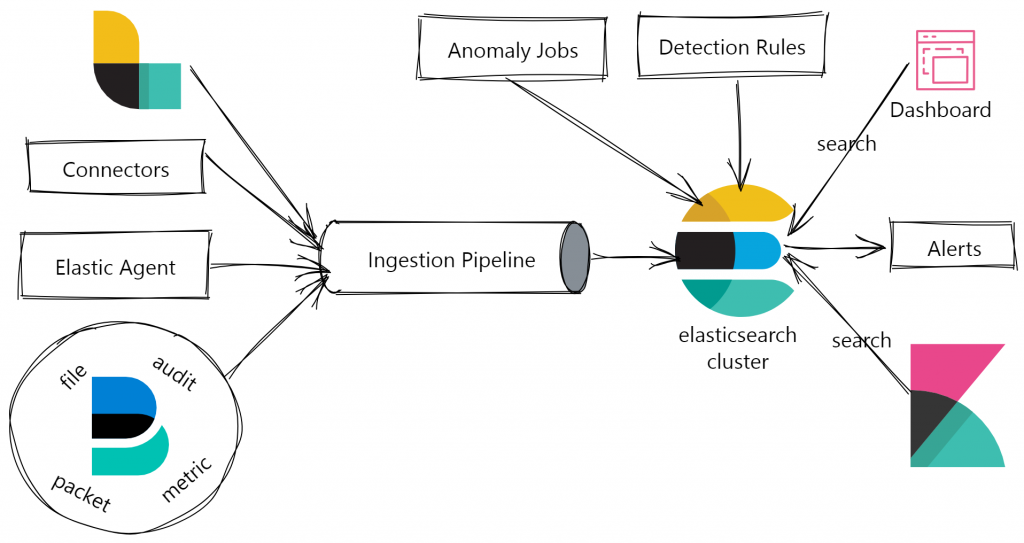
![Cloud Native Vulnerability Management Dashboard | Elastic Security Solution [8.11] | Elastic Cloud Native Vulnerability Management Dashboard | Elastic Security Solution [8.11] | Elastic](https://www.elastic.co/guide/en/security/current/images/vuln-management-dashboard.png)
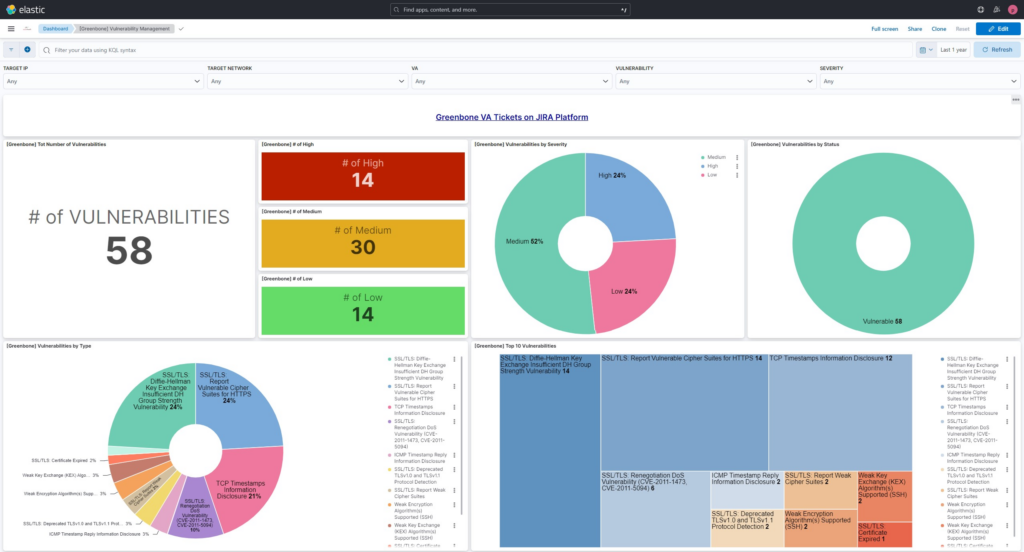


.png)
