près de 33 % des cyberattaques dans le cloud exploitent les failles des accès protégés par des identifiants - PereLaFouine

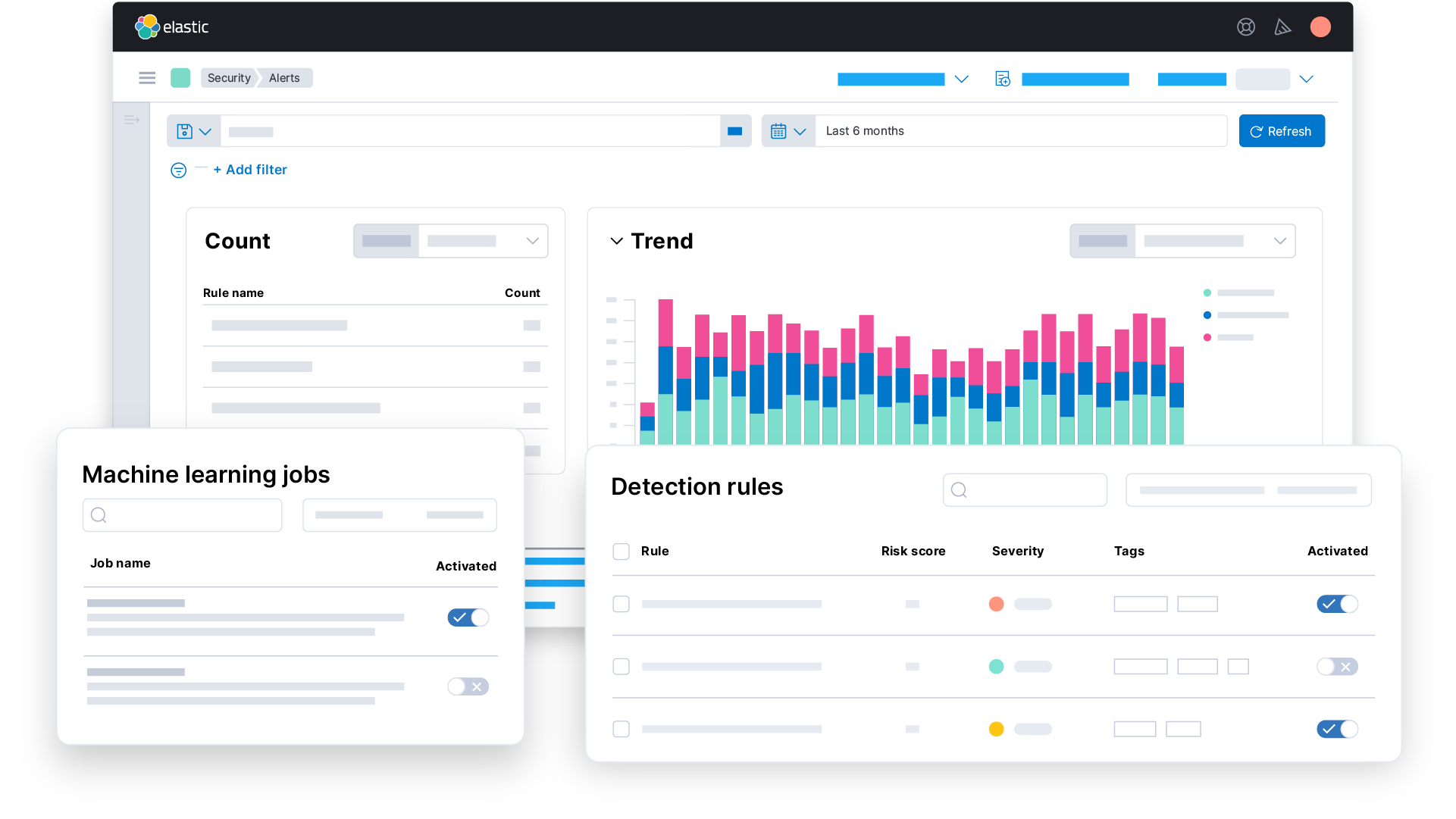
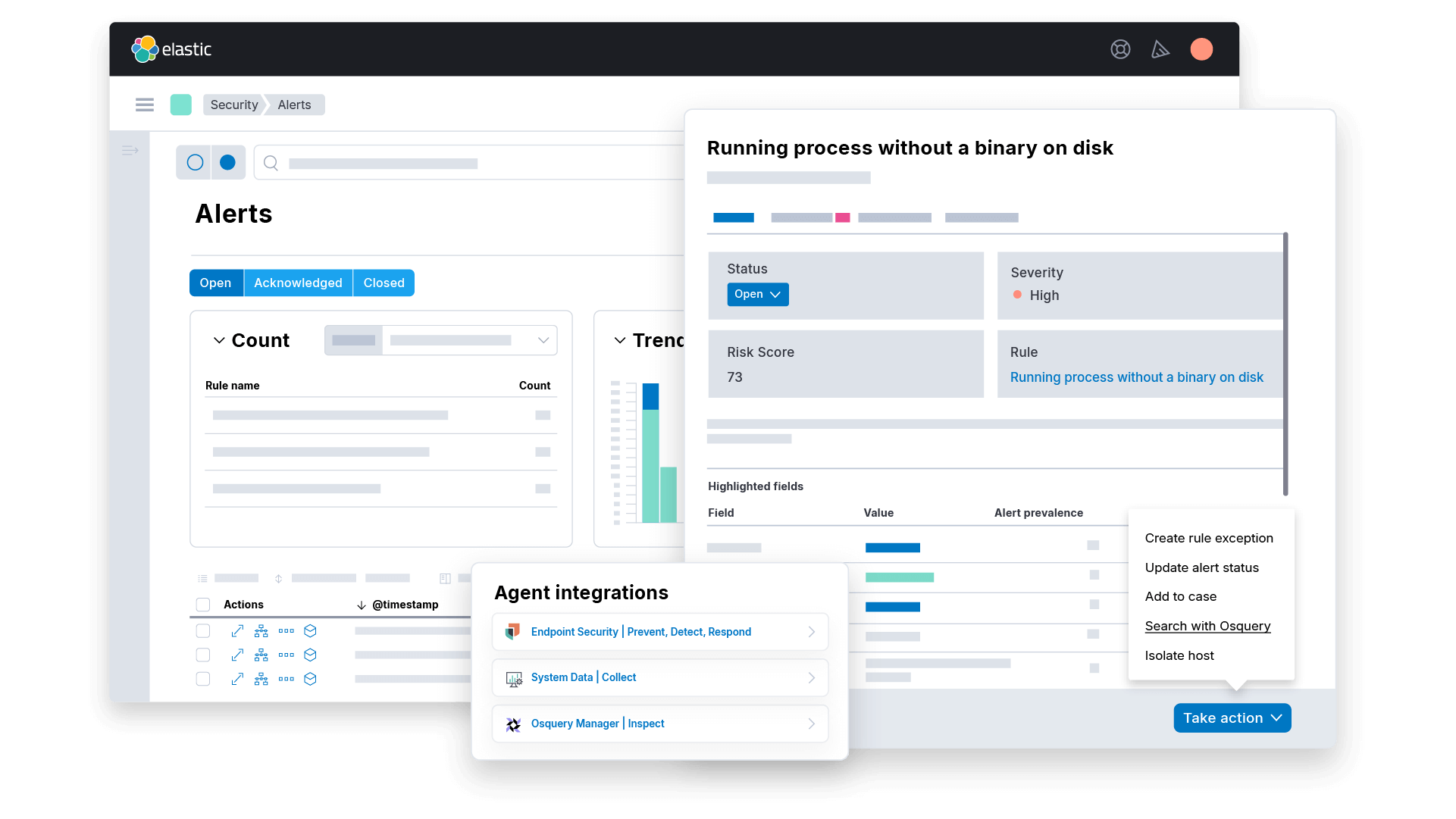
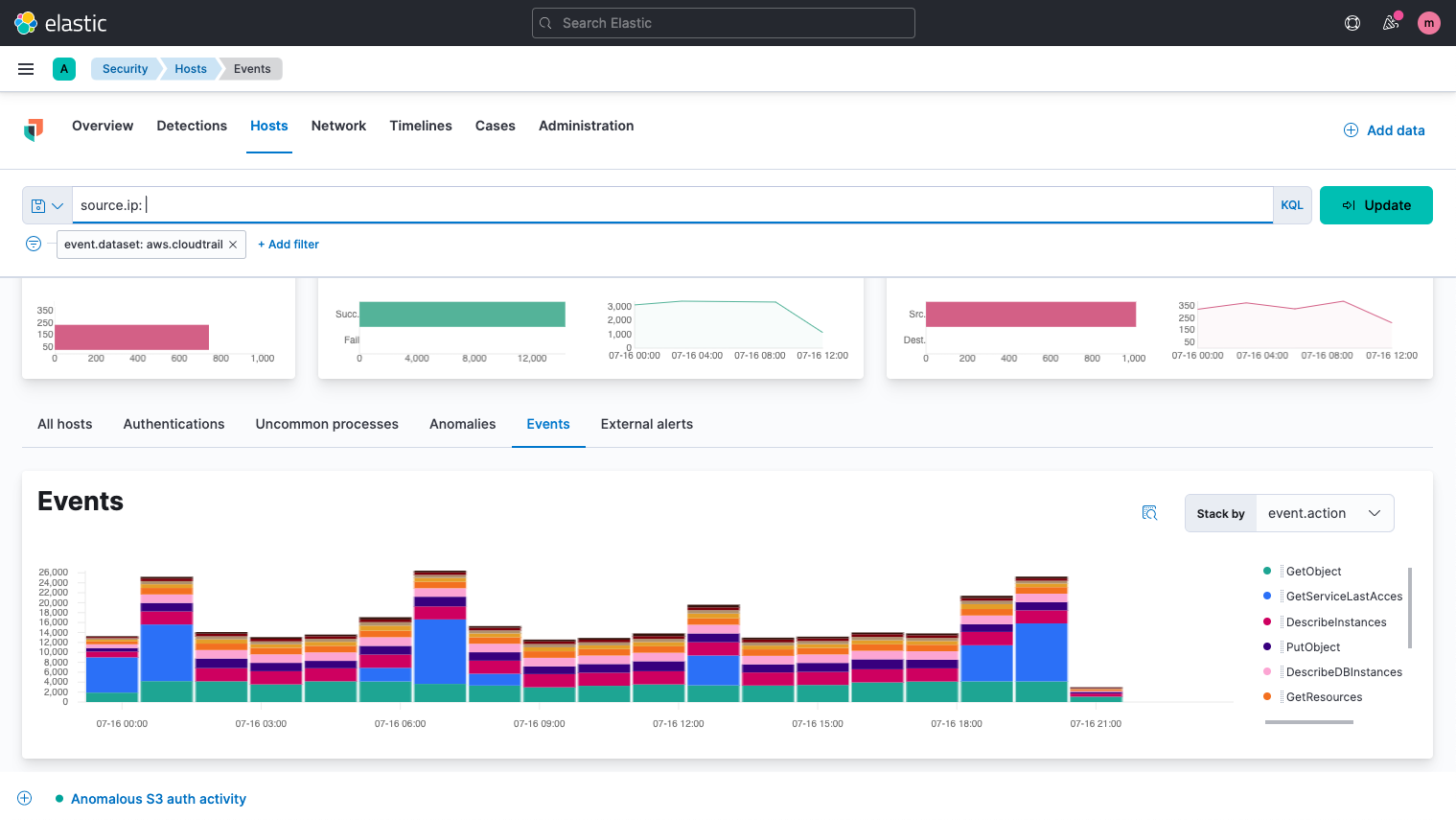
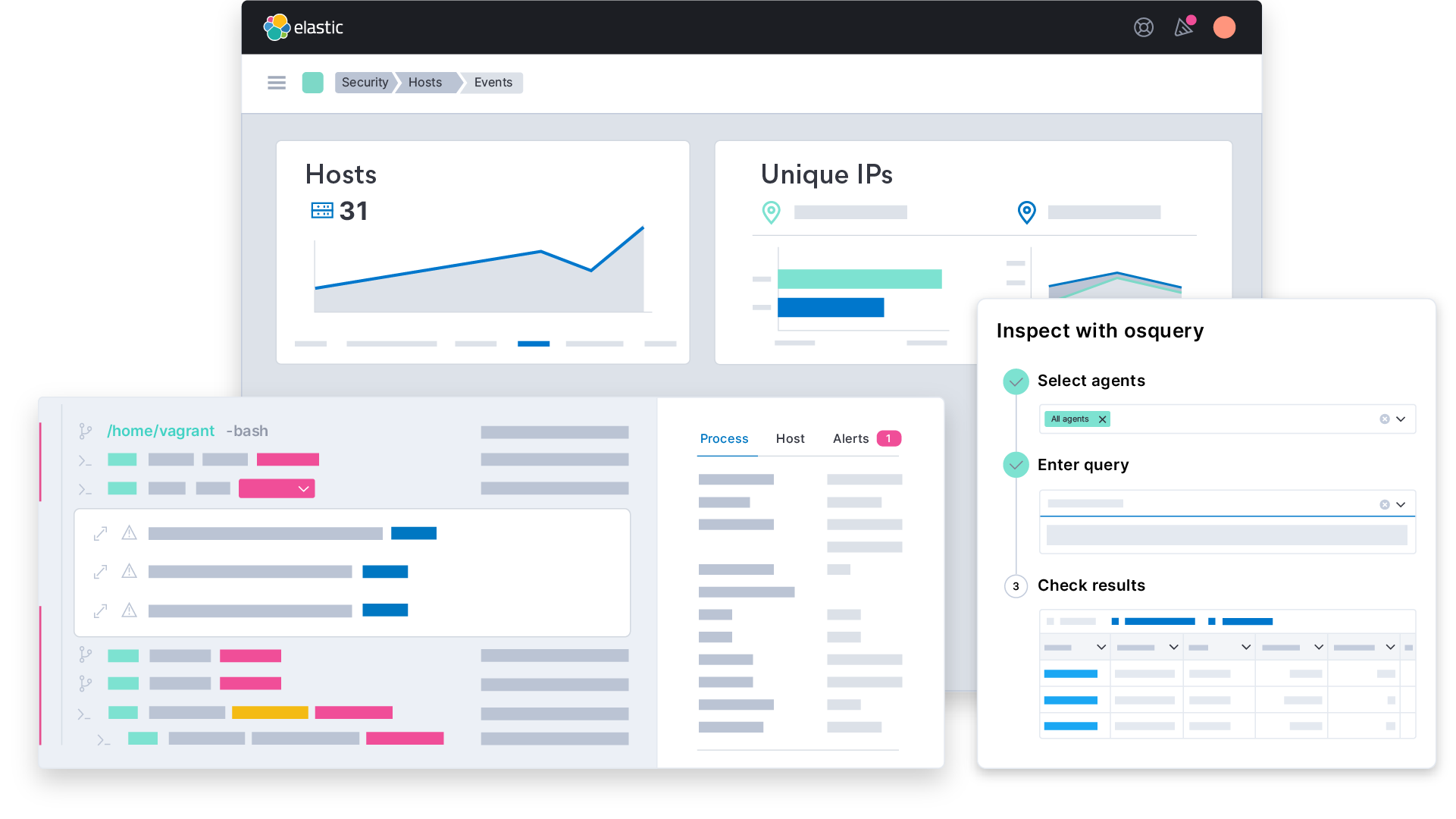
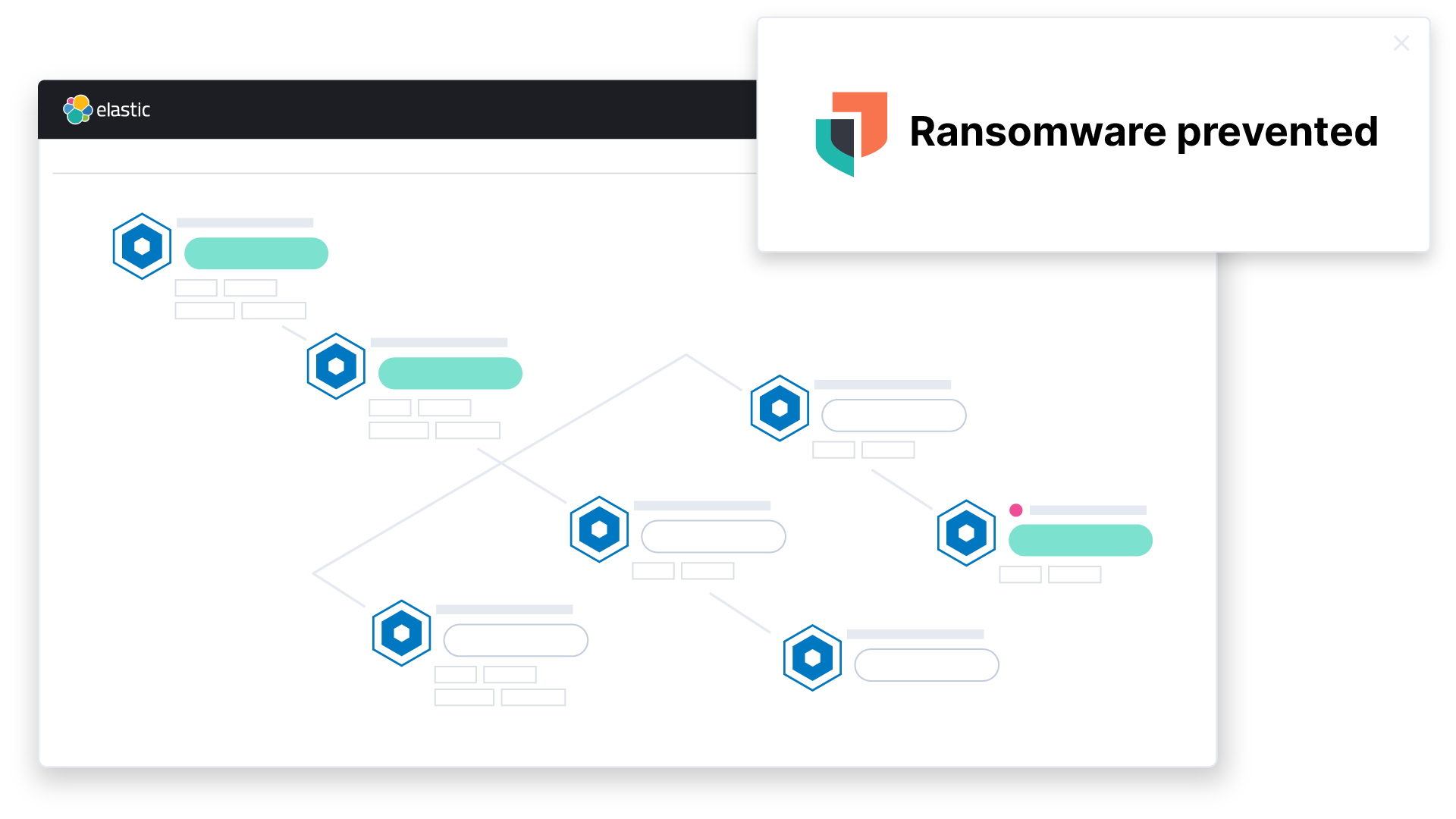
Elastic - At #ElasticON Global, the #ElasticSecurity team shared how the future of Limitless XDR unifies the capabilities of SIEM, endpoint security, and cloud security. Catch a written recap of our Security
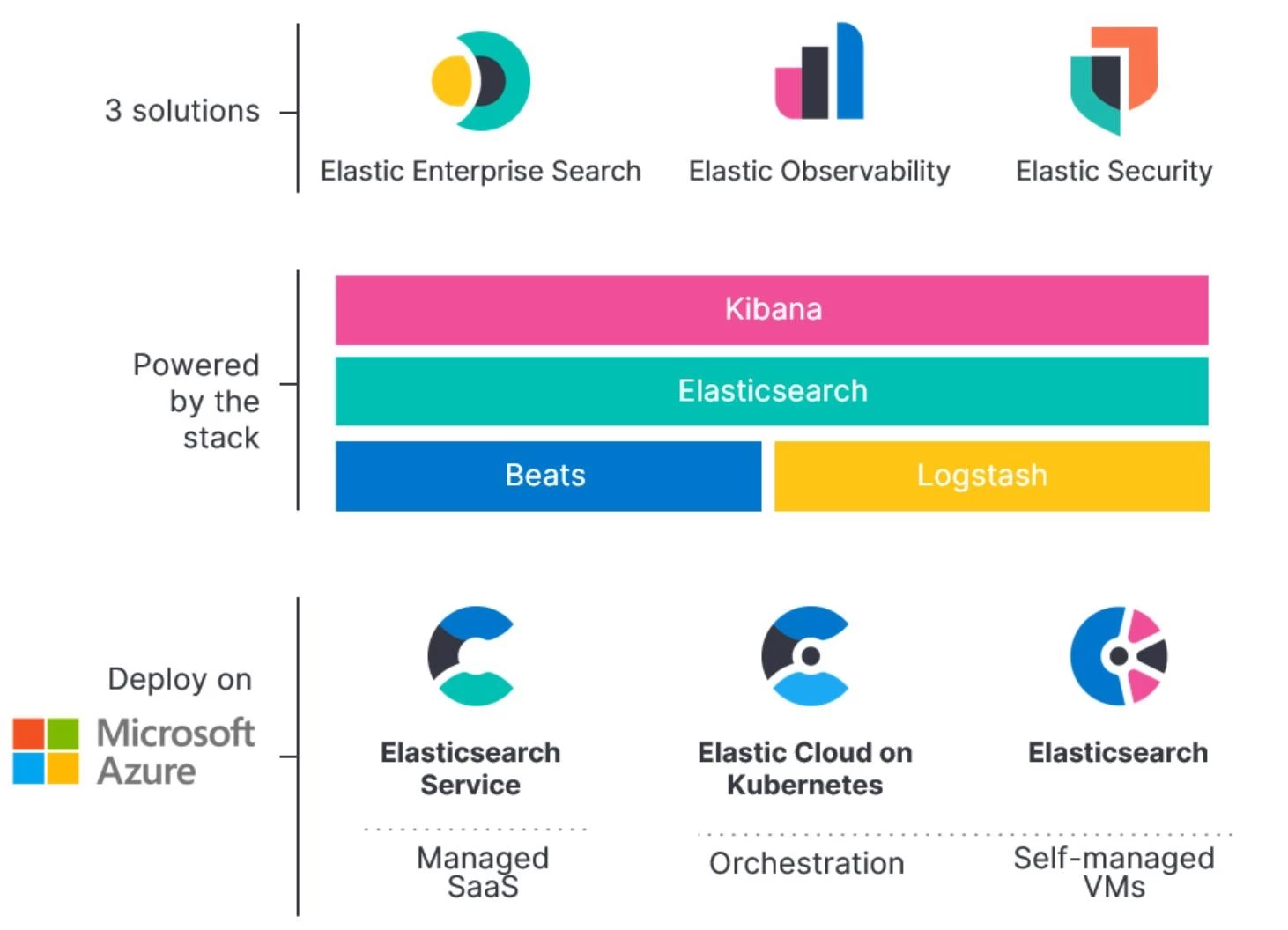
Search made simple: native Elastic integration with Azure—now in preview | Blog Azure | Microsoft Azure



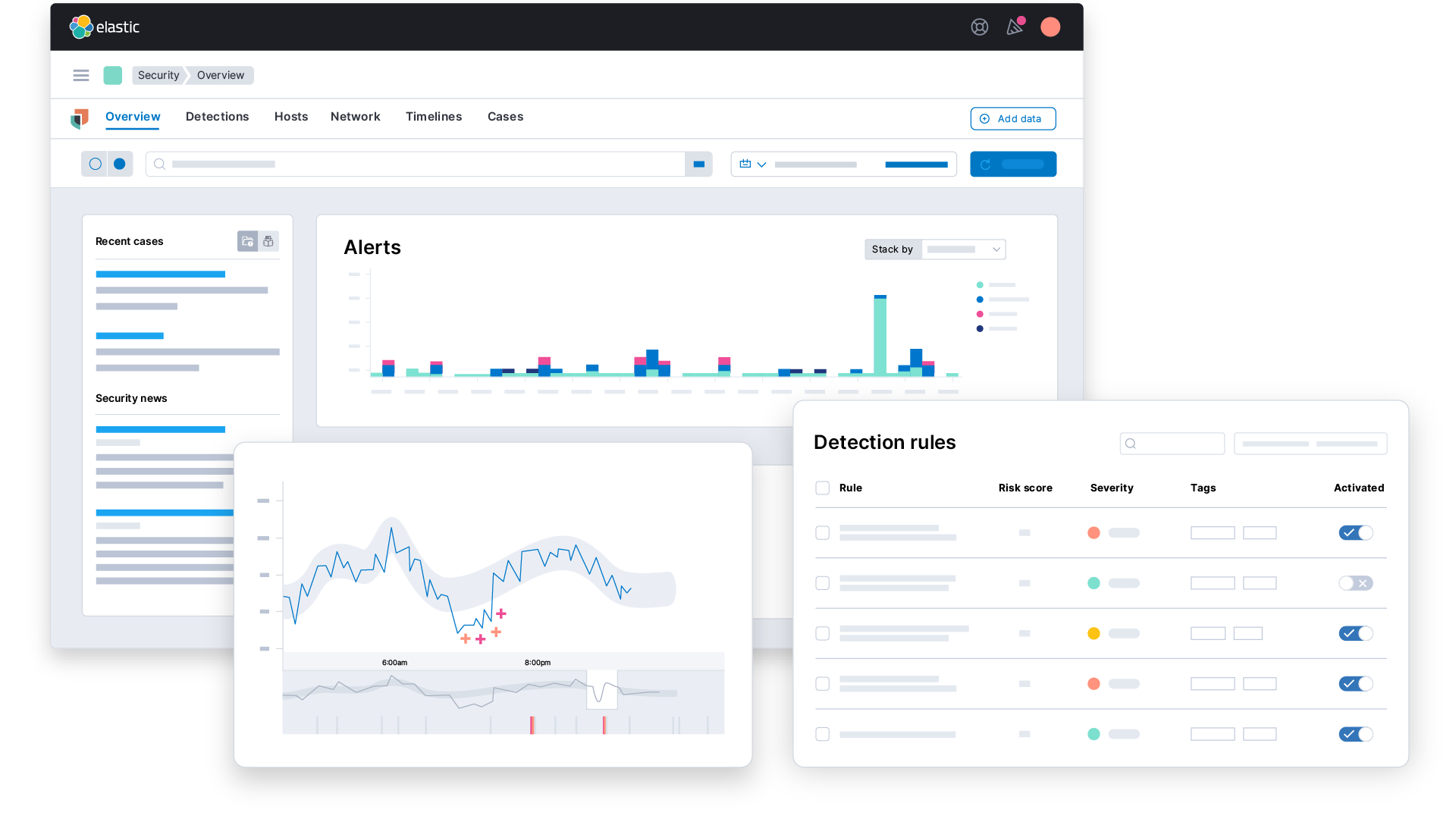

![Elastic Security overview | Elastic Security Solution [8.11] | Elastic Elastic Security overview | Elastic Security Solution [8.11] | Elastic](https://www.elastic.co/guide/en/security/current/images/workflow.png)